
How Colgate-Palmolive boosted developer security skills and created a secure coding culture
TL;TR

About Colgate-Palmolive
Colgate-Palmolive Company is a marquis consumer products brand known and loved across households everywhere. Despite being more than two centuries old, they are an innovative growth company leveraging digital to reimagine a healthier future for people, their pets, and the planet.
Situation
Colgate-Palmolive, just like nearly every other organization, is going through a digital transformation to better serve its customers, and this has led to a shift in how the organization approaches application security.
Alex Schuchman, CISO at Colgate-Palmolive, puts it this way:
“It is very important to us that we are protecting our customer’s data and therefore are able to build trust—not just in our products but in the digital interactions our customers have with us."
But for Alex, the challenge was to secure the root source of potential customer data breaches—the code itself.
“Working on the build side of applications was really helpful when I made the switch over to my role as CISO. I understand the pain of getting tickets back from AppSec or the frustration of missing deadlines because of re-work. As a result, my goal as CISO hasn't just been increasing security in the software development lifecycle, but also streamlining how it is implemented.”
Action
Colgate-Palmolive approached this challenge by breaking up its security training into smaller, bite-sized chunks. This made it more palatable for developers so they could fit it into their workflow, instead of the long, monolithic compliance training they were used to. By leveraging Secure Code Warrior’s agile, in-context approach to secure code learning, developers were able to understand vulnerabilities in the context of their real-life projects – leading to higher engagement and long-term retention of secure coding skills.
“I wanted to roll out these best practices while keeping the developers engaged,” says Alex. “We still have mandated critical parts of the program but keeping the training manageable and listening to developer feedback has helped the program be successful.”
Colgate-Palmolive implemented an Okta workflow that gates the GitHub repository, allowing only developers who've passed specific SCW assessments access for pull requests, as depicted in the diagram below.

Results
According to Alex, “We understood that to optimize for success we needed to have our developers on-board from the start. So we made sure the developers knew they would be a critical part of the success of the program. As a result, we found that there was a much better relationship between our security team and our developers, and it really felt like we were working together as a team on the program. We are continuing to expand and scale the security maturity program, building on the success we have already enjoyed.”
Key takeaways
- Clearly define program goals and emphasize developer input and engagement. Developers are more likely to buy-in to a secure code learning program that is built into their workflow and integrated with the dev tools they use every day.
- Using an SSO tool such as Okta to gate the code repository incentivizes the team. Only developers with a passing score on specific SCW courses and assessment are permitted to make pull requests.
- Over time, build a security culture that promotes a strong working relationship between AppSec and Development teams.

Discover how retail giant Colgate-Palmolive reshaped its application security during its digital transformation journey. Facing challenges in secure coding, they innovated their approach by integrating bite-sized, in-context learning into the developer workflow.

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demo
TL;TR

About Colgate-Palmolive
Colgate-Palmolive Company is a marquis consumer products brand known and loved across households everywhere. Despite being more than two centuries old, they are an innovative growth company leveraging digital to reimagine a healthier future for people, their pets, and the planet.
Situation
Colgate-Palmolive, just like nearly every other organization, is going through a digital transformation to better serve its customers, and this has led to a shift in how the organization approaches application security.
Alex Schuchman, CISO at Colgate-Palmolive, puts it this way:
“It is very important to us that we are protecting our customer’s data and therefore are able to build trust—not just in our products but in the digital interactions our customers have with us."
But for Alex, the challenge was to secure the root source of potential customer data breaches—the code itself.
“Working on the build side of applications was really helpful when I made the switch over to my role as CISO. I understand the pain of getting tickets back from AppSec or the frustration of missing deadlines because of re-work. As a result, my goal as CISO hasn't just been increasing security in the software development lifecycle, but also streamlining how it is implemented.”
Action
Colgate-Palmolive approached this challenge by breaking up its security training into smaller, bite-sized chunks. This made it more palatable for developers so they could fit it into their workflow, instead of the long, monolithic compliance training they were used to. By leveraging Secure Code Warrior’s agile, in-context approach to secure code learning, developers were able to understand vulnerabilities in the context of their real-life projects – leading to higher engagement and long-term retention of secure coding skills.
“I wanted to roll out these best practices while keeping the developers engaged,” says Alex. “We still have mandated critical parts of the program but keeping the training manageable and listening to developer feedback has helped the program be successful.”
Colgate-Palmolive implemented an Okta workflow that gates the GitHub repository, allowing only developers who've passed specific SCW assessments access for pull requests, as depicted in the diagram below.

Results
According to Alex, “We understood that to optimize for success we needed to have our developers on-board from the start. So we made sure the developers knew they would be a critical part of the success of the program. As a result, we found that there was a much better relationship between our security team and our developers, and it really felt like we were working together as a team on the program. We are continuing to expand and scale the security maturity program, building on the success we have already enjoyed.”
Key takeaways
- Clearly define program goals and emphasize developer input and engagement. Developers are more likely to buy-in to a secure code learning program that is built into their workflow and integrated with the dev tools they use every day.
- Using an SSO tool such as Okta to gate the code repository incentivizes the team. Only developers with a passing score on specific SCW courses and assessment are permitted to make pull requests.
- Over time, build a security culture that promotes a strong working relationship between AppSec and Development teams.
TL;TR

About Colgate-Palmolive
Colgate-Palmolive Company is a marquis consumer products brand known and loved across households everywhere. Despite being more than two centuries old, they are an innovative growth company leveraging digital to reimagine a healthier future for people, their pets, and the planet.
Situation
Colgate-Palmolive, just like nearly every other organization, is going through a digital transformation to better serve its customers, and this has led to a shift in how the organization approaches application security.
Alex Schuchman, CISO at Colgate-Palmolive, puts it this way:
“It is very important to us that we are protecting our customer’s data and therefore are able to build trust—not just in our products but in the digital interactions our customers have with us."
But for Alex, the challenge was to secure the root source of potential customer data breaches—the code itself.
“Working on the build side of applications was really helpful when I made the switch over to my role as CISO. I understand the pain of getting tickets back from AppSec or the frustration of missing deadlines because of re-work. As a result, my goal as CISO hasn't just been increasing security in the software development lifecycle, but also streamlining how it is implemented.”
Action
Colgate-Palmolive approached this challenge by breaking up its security training into smaller, bite-sized chunks. This made it more palatable for developers so they could fit it into their workflow, instead of the long, monolithic compliance training they were used to. By leveraging Secure Code Warrior’s agile, in-context approach to secure code learning, developers were able to understand vulnerabilities in the context of their real-life projects – leading to higher engagement and long-term retention of secure coding skills.
“I wanted to roll out these best practices while keeping the developers engaged,” says Alex. “We still have mandated critical parts of the program but keeping the training manageable and listening to developer feedback has helped the program be successful.”
Colgate-Palmolive implemented an Okta workflow that gates the GitHub repository, allowing only developers who've passed specific SCW assessments access for pull requests, as depicted in the diagram below.

Results
According to Alex, “We understood that to optimize for success we needed to have our developers on-board from the start. So we made sure the developers knew they would be a critical part of the success of the program. As a result, we found that there was a much better relationship between our security team and our developers, and it really felt like we were working together as a team on the program. We are continuing to expand and scale the security maturity program, building on the success we have already enjoyed.”
Key takeaways
- Clearly define program goals and emphasize developer input and engagement. Developers are more likely to buy-in to a secure code learning program that is built into their workflow and integrated with the dev tools they use every day.
- Using an SSO tool such as Okta to gate the code repository incentivizes the team. Only developers with a passing score on specific SCW courses and assessment are permitted to make pull requests.
- Over time, build a security culture that promotes a strong working relationship between AppSec and Development teams.

Click on the link below and download the PDF of this resource.
Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
View reportBook a demoTL;TR

About Colgate-Palmolive
Colgate-Palmolive Company is a marquis consumer products brand known and loved across households everywhere. Despite being more than two centuries old, they are an innovative growth company leveraging digital to reimagine a healthier future for people, their pets, and the planet.
Situation
Colgate-Palmolive, just like nearly every other organization, is going through a digital transformation to better serve its customers, and this has led to a shift in how the organization approaches application security.
Alex Schuchman, CISO at Colgate-Palmolive, puts it this way:
“It is very important to us that we are protecting our customer’s data and therefore are able to build trust—not just in our products but in the digital interactions our customers have with us."
But for Alex, the challenge was to secure the root source of potential customer data breaches—the code itself.
“Working on the build side of applications was really helpful when I made the switch over to my role as CISO. I understand the pain of getting tickets back from AppSec or the frustration of missing deadlines because of re-work. As a result, my goal as CISO hasn't just been increasing security in the software development lifecycle, but also streamlining how it is implemented.”
Action
Colgate-Palmolive approached this challenge by breaking up its security training into smaller, bite-sized chunks. This made it more palatable for developers so they could fit it into their workflow, instead of the long, monolithic compliance training they were used to. By leveraging Secure Code Warrior’s agile, in-context approach to secure code learning, developers were able to understand vulnerabilities in the context of their real-life projects – leading to higher engagement and long-term retention of secure coding skills.
“I wanted to roll out these best practices while keeping the developers engaged,” says Alex. “We still have mandated critical parts of the program but keeping the training manageable and listening to developer feedback has helped the program be successful.”
Colgate-Palmolive implemented an Okta workflow that gates the GitHub repository, allowing only developers who've passed specific SCW assessments access for pull requests, as depicted in the diagram below.

Results
According to Alex, “We understood that to optimize for success we needed to have our developers on-board from the start. So we made sure the developers knew they would be a critical part of the success of the program. As a result, we found that there was a much better relationship between our security team and our developers, and it really felt like we were working together as a team on the program. We are continuing to expand and scale the security maturity program, building on the success we have already enjoyed.”
Key takeaways
- Clearly define program goals and emphasize developer input and engagement. Developers are more likely to buy-in to a secure code learning program that is built into their workflow and integrated with the dev tools they use every day.
- Using an SSO tool such as Okta to gate the code repository incentivizes the team. Only developers with a passing score on specific SCW courses and assessment are permitted to make pull requests.
- Over time, build a security culture that promotes a strong working relationship between AppSec and Development teams.
Table of contents

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demoDownloadResources to get you started
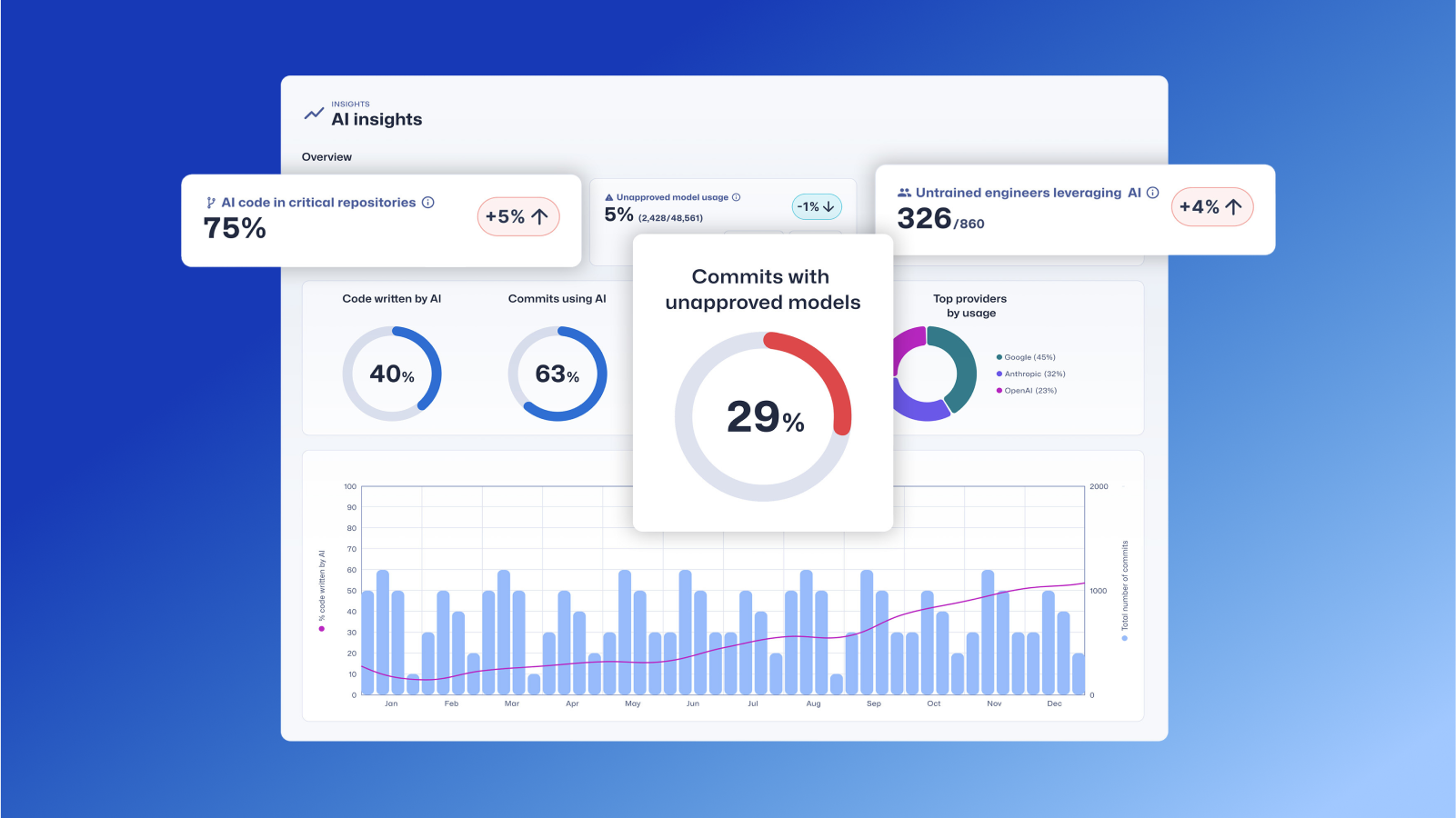
Trust Agent: AI by Secure Code Warrior
This one-pager introduces SCW Trust Agent: AI, a new set of capabilities that provide deep observability and governance over AI coding tools. Learn how our solution uniquely correlates AI tool usage with developer skills to help you manage risk, optimize your SDLC, and ensure every line of AI-generated code is secure.











.png)


.avif)
