Introducing the 10 Enablers of Success
People and Processes
Anyone can build a secure coding program, but achieving lasting success is a more complex endeavor. The challenge lies not just in choosing a platform or launching the program, but also in effectively integrating it within an organization that often has diverse teams with competing interests.
Whether the program’s driving force is AppSec, L&D, DevOps, or Engineering itself, both the people and processes play a part in creating a successful program.
This is where the 10 Enablers of Success come in. This 12-part blog series will unveil our proven operational blueprint for any organization to build, sustain, and scale a highly effective secure coding program.
Drawing on more than ten years of experience with leading organizations, Secure Code Warrior’s Customer Success team–with key contributor Jim Loughran–has identified these 10 factors as crucial elements to drive adoption, usage, and developer "stickiness" and therefore value over time.
The 10 Enablers of Success
Over the next ten blog posts, we will dive deeply into each of these enablers. Successfully implementing these steps helps a program through critical maturity stages, transforming developers into the "first line of defense" for your organization.
The Enablers include the following:
- Defined & Measurable Success Criteria: Establish program objectives that are directly linked to business outcomes to increase relevance and trace return on investment.
- Senior Leadership Sponsorship: Ensure C-Suite/Executive buy-in to help drive a smooth program rollout and secure interdepartmental support.
- Developer Communications Plan: Maintain an ongoing, exciting, and informative communication stream to keep developers engaged throughout the program.
- Low Barrier to User Access: Enable quick and easy developer access to relevant platforms, utilizing tools like SSO.
- Certification Programs: Implement multi-level programs to manage developer progression and provide meaningful achievements through continuous learning.
- Regular Reporting to Leadership: Provide consistent, relevant updates to share progress, celebrate wins, and showcase impact for continued executive buy-in.
- Developer Recognition: Share wins, tournament results, and call out successes loudly to celebrate and encourage developer achievement.
- Branding Your Program: Embed a recognizable brand, name, or acronym (like ASC for Application Security Champion) within the developer community for continued program socialization.
- Developer Ecosystem Integration: Use APIs and integrations to enrich data and embed secure code training into existing development workflows (e.g., JIRA or LMS integrations).
- Training Linked to Career Progression: Partner with HR/People teams to embed training (like certifications) into developer performance goals, reviews, or annual bonuses.
The Path to Program Maturity
Regardless of where you are in the building of your secure coding program, the implementation of these enablers directly correlates with the maturity level of your program. Program Maturity can be measured based on how many enablers are in play.
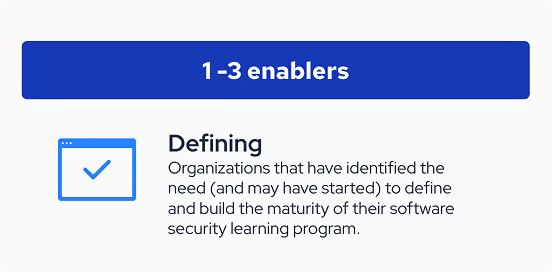
Having 1-3 enablers implemented indicates an organization is still defining its secure coding program. It is likely that the program is still in its infancy or even still being rolled out. There are opportunities for maturing as the program grows.
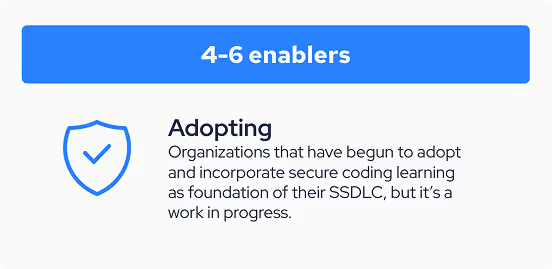
Having 4-6 enablers implemented means a program is in its adopting stage. The program is continually being integrated into the organization’s security culture and is maturing or optimizing “on the way” to full adoption.
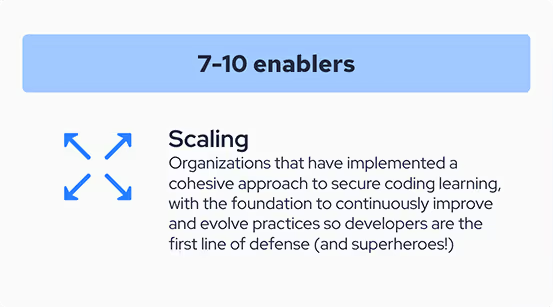
Finally, having 7-10 enablers implemented means a program is scaling.
At this stage, security is deeply ingrained into the organization’s culture and training is linked not only to developers’ ecosystem of tools, but also to their sense of accomplishment and career progression.
Whatever stage you are at, follow along as we continue to explore each of the enablers in depth, starting with Enabler 1: Defined & Measurable Success Criteria.
Have additional questions?
Customers can reach out to account team members or to support@securecodewarrior.com. Prospective customers can speak to someone on our sales team by contacting us here.


Secure Code Warrior’s 10 Enablers guide organizations in building lasting secure coding programs by focusing on people, process, and program maturity stages.

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demoKatelynd Trinidad, Curriculum & Onboarding Manager at SCW, is a customer success professional with more than 6 years of experience enabling customers with programatic best practices and technical how to’s.


People and Processes
Anyone can build a secure coding program, but achieving lasting success is a more complex endeavor. The challenge lies not just in choosing a platform or launching the program, but also in effectively integrating it within an organization that often has diverse teams with competing interests.
Whether the program’s driving force is AppSec, L&D, DevOps, or Engineering itself, both the people and processes play a part in creating a successful program.
This is where the 10 Enablers of Success come in. This 12-part blog series will unveil our proven operational blueprint for any organization to build, sustain, and scale a highly effective secure coding program.
Drawing on more than ten years of experience with leading organizations, Secure Code Warrior’s Customer Success team–with key contributor Jim Loughran–has identified these 10 factors as crucial elements to drive adoption, usage, and developer "stickiness" and therefore value over time.
The 10 Enablers of Success
Over the next ten blog posts, we will dive deeply into each of these enablers. Successfully implementing these steps helps a program through critical maturity stages, transforming developers into the "first line of defense" for your organization.
The Enablers include the following:
- Defined & Measurable Success Criteria: Establish program objectives that are directly linked to business outcomes to increase relevance and trace return on investment.
- Senior Leadership Sponsorship: Ensure C-Suite/Executive buy-in to help drive a smooth program rollout and secure interdepartmental support.
- Developer Communications Plan: Maintain an ongoing, exciting, and informative communication stream to keep developers engaged throughout the program.
- Low Barrier to User Access: Enable quick and easy developer access to relevant platforms, utilizing tools like SSO.
- Certification Programs: Implement multi-level programs to manage developer progression and provide meaningful achievements through continuous learning.
- Regular Reporting to Leadership: Provide consistent, relevant updates to share progress, celebrate wins, and showcase impact for continued executive buy-in.
- Developer Recognition: Share wins, tournament results, and call out successes loudly to celebrate and encourage developer achievement.
- Branding Your Program: Embed a recognizable brand, name, or acronym (like ASC for Application Security Champion) within the developer community for continued program socialization.
- Developer Ecosystem Integration: Use APIs and integrations to enrich data and embed secure code training into existing development workflows (e.g., JIRA or LMS integrations).
- Training Linked to Career Progression: Partner with HR/People teams to embed training (like certifications) into developer performance goals, reviews, or annual bonuses.
The Path to Program Maturity
Regardless of where you are in the building of your secure coding program, the implementation of these enablers directly correlates with the maturity level of your program. Program Maturity can be measured based on how many enablers are in play.
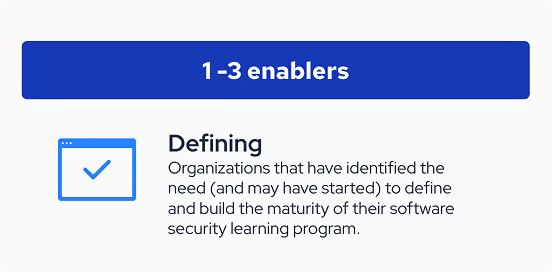
Having 1-3 enablers implemented indicates an organization is still defining its secure coding program. It is likely that the program is still in its infancy or even still being rolled out. There are opportunities for maturing as the program grows.
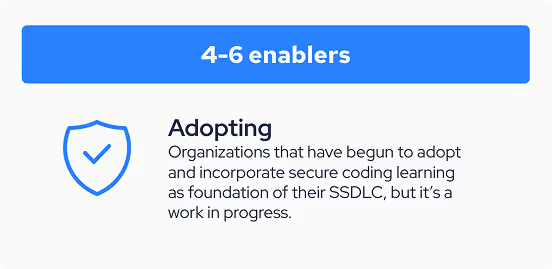
Having 4-6 enablers implemented means a program is in its adopting stage. The program is continually being integrated into the organization’s security culture and is maturing or optimizing “on the way” to full adoption.
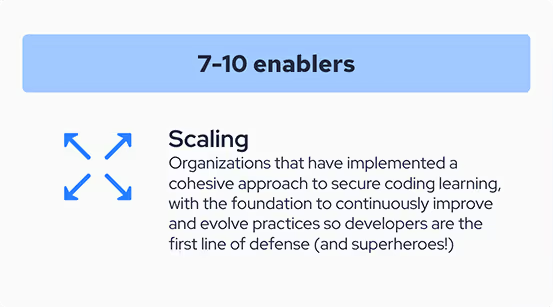
Finally, having 7-10 enablers implemented means a program is scaling.
At this stage, security is deeply ingrained into the organization’s culture and training is linked not only to developers’ ecosystem of tools, but also to their sense of accomplishment and career progression.
Whatever stage you are at, follow along as we continue to explore each of the enablers in depth, starting with Enabler 1: Defined & Measurable Success Criteria.
Have additional questions?
Customers can reach out to account team members or to support@securecodewarrior.com. Prospective customers can speak to someone on our sales team by contacting us here.

People and Processes
Anyone can build a secure coding program, but achieving lasting success is a more complex endeavor. The challenge lies not just in choosing a platform or launching the program, but also in effectively integrating it within an organization that often has diverse teams with competing interests.
Whether the program’s driving force is AppSec, L&D, DevOps, or Engineering itself, both the people and processes play a part in creating a successful program.
This is where the 10 Enablers of Success come in. This 12-part blog series will unveil our proven operational blueprint for any organization to build, sustain, and scale a highly effective secure coding program.
Drawing on more than ten years of experience with leading organizations, Secure Code Warrior’s Customer Success team–with key contributor Jim Loughran–has identified these 10 factors as crucial elements to drive adoption, usage, and developer "stickiness" and therefore value over time.
The 10 Enablers of Success
Over the next ten blog posts, we will dive deeply into each of these enablers. Successfully implementing these steps helps a program through critical maturity stages, transforming developers into the "first line of defense" for your organization.
The Enablers include the following:
- Defined & Measurable Success Criteria: Establish program objectives that are directly linked to business outcomes to increase relevance and trace return on investment.
- Senior Leadership Sponsorship: Ensure C-Suite/Executive buy-in to help drive a smooth program rollout and secure interdepartmental support.
- Developer Communications Plan: Maintain an ongoing, exciting, and informative communication stream to keep developers engaged throughout the program.
- Low Barrier to User Access: Enable quick and easy developer access to relevant platforms, utilizing tools like SSO.
- Certification Programs: Implement multi-level programs to manage developer progression and provide meaningful achievements through continuous learning.
- Regular Reporting to Leadership: Provide consistent, relevant updates to share progress, celebrate wins, and showcase impact for continued executive buy-in.
- Developer Recognition: Share wins, tournament results, and call out successes loudly to celebrate and encourage developer achievement.
- Branding Your Program: Embed a recognizable brand, name, or acronym (like ASC for Application Security Champion) within the developer community for continued program socialization.
- Developer Ecosystem Integration: Use APIs and integrations to enrich data and embed secure code training into existing development workflows (e.g., JIRA or LMS integrations).
- Training Linked to Career Progression: Partner with HR/People teams to embed training (like certifications) into developer performance goals, reviews, or annual bonuses.
The Path to Program Maturity
Regardless of where you are in the building of your secure coding program, the implementation of these enablers directly correlates with the maturity level of your program. Program Maturity can be measured based on how many enablers are in play.
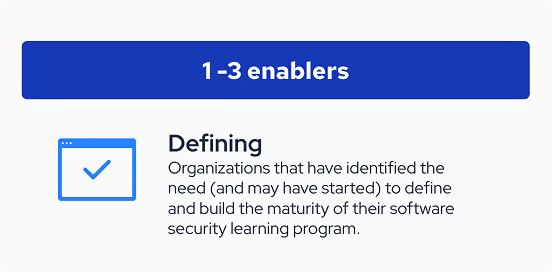
Having 1-3 enablers implemented indicates an organization is still defining its secure coding program. It is likely that the program is still in its infancy or even still being rolled out. There are opportunities for maturing as the program grows.
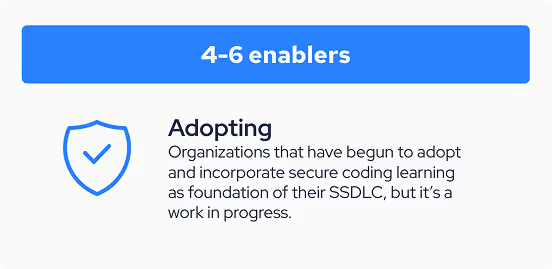
Having 4-6 enablers implemented means a program is in its adopting stage. The program is continually being integrated into the organization’s security culture and is maturing or optimizing “on the way” to full adoption.
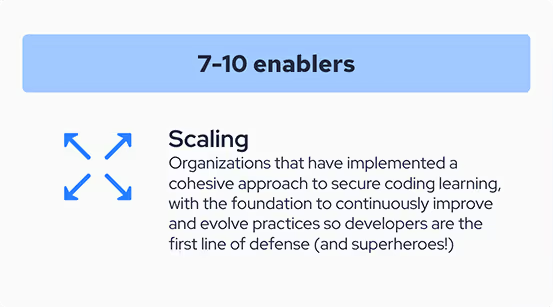
Finally, having 7-10 enablers implemented means a program is scaling.
At this stage, security is deeply ingrained into the organization’s culture and training is linked not only to developers’ ecosystem of tools, but also to their sense of accomplishment and career progression.
Whatever stage you are at, follow along as we continue to explore each of the enablers in depth, starting with Enabler 1: Defined & Measurable Success Criteria.
Have additional questions?
Customers can reach out to account team members or to support@securecodewarrior.com. Prospective customers can speak to someone on our sales team by contacting us here.

Click on the link below and download the PDF of this resource.
Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
View reportBook a demoKatelynd Trinidad, Curriculum & Onboarding Manager at SCW, is a customer success professional with more than 6 years of experience enabling customers with programatic best practices and technical how to’s.
People and Processes
Anyone can build a secure coding program, but achieving lasting success is a more complex endeavor. The challenge lies not just in choosing a platform or launching the program, but also in effectively integrating it within an organization that often has diverse teams with competing interests.
Whether the program’s driving force is AppSec, L&D, DevOps, or Engineering itself, both the people and processes play a part in creating a successful program.
This is where the 10 Enablers of Success come in. This 12-part blog series will unveil our proven operational blueprint for any organization to build, sustain, and scale a highly effective secure coding program.
Drawing on more than ten years of experience with leading organizations, Secure Code Warrior’s Customer Success team–with key contributor Jim Loughran–has identified these 10 factors as crucial elements to drive adoption, usage, and developer "stickiness" and therefore value over time.
The 10 Enablers of Success
Over the next ten blog posts, we will dive deeply into each of these enablers. Successfully implementing these steps helps a program through critical maturity stages, transforming developers into the "first line of defense" for your organization.
The Enablers include the following:
- Defined & Measurable Success Criteria: Establish program objectives that are directly linked to business outcomes to increase relevance and trace return on investment.
- Senior Leadership Sponsorship: Ensure C-Suite/Executive buy-in to help drive a smooth program rollout and secure interdepartmental support.
- Developer Communications Plan: Maintain an ongoing, exciting, and informative communication stream to keep developers engaged throughout the program.
- Low Barrier to User Access: Enable quick and easy developer access to relevant platforms, utilizing tools like SSO.
- Certification Programs: Implement multi-level programs to manage developer progression and provide meaningful achievements through continuous learning.
- Regular Reporting to Leadership: Provide consistent, relevant updates to share progress, celebrate wins, and showcase impact for continued executive buy-in.
- Developer Recognition: Share wins, tournament results, and call out successes loudly to celebrate and encourage developer achievement.
- Branding Your Program: Embed a recognizable brand, name, or acronym (like ASC for Application Security Champion) within the developer community for continued program socialization.
- Developer Ecosystem Integration: Use APIs and integrations to enrich data and embed secure code training into existing development workflows (e.g., JIRA or LMS integrations).
- Training Linked to Career Progression: Partner with HR/People teams to embed training (like certifications) into developer performance goals, reviews, or annual bonuses.
The Path to Program Maturity
Regardless of where you are in the building of your secure coding program, the implementation of these enablers directly correlates with the maturity level of your program. Program Maturity can be measured based on how many enablers are in play.
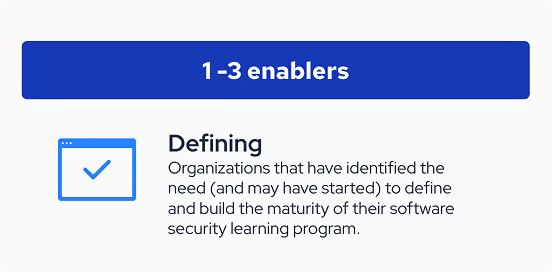
Having 1-3 enablers implemented indicates an organization is still defining its secure coding program. It is likely that the program is still in its infancy or even still being rolled out. There are opportunities for maturing as the program grows.
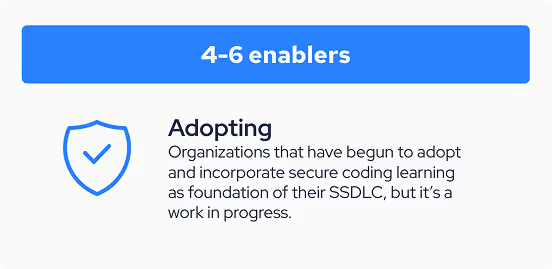
Having 4-6 enablers implemented means a program is in its adopting stage. The program is continually being integrated into the organization’s security culture and is maturing or optimizing “on the way” to full adoption.
Finally, having 7-10 enablers implemented means a program is scaling.
At this stage, security is deeply ingrained into the organization’s culture and training is linked not only to developers’ ecosystem of tools, but also to their sense of accomplishment and career progression.
Whatever stage you are at, follow along as we continue to explore each of the enablers in depth, starting with Enabler 1: Defined & Measurable Success Criteria.
Have additional questions?
Customers can reach out to account team members or to support@securecodewarrior.com. Prospective customers can speak to someone on our sales team by contacting us here.
Table of contents

Secure Code Warrior is here for your organization to help you secure code across the entire software development lifecycle and create a culture in which cybersecurity is top of mind. Whether you’re an AppSec Manager, Developer, CISO, or anyone involved in security, we can help your organization reduce risks associated with insecure code.
Book a demoDownloadResources to get you started
Trust Agent:AI - Secure and scale AI-Drive development
AI is writing code. Who’s governing it? With up to 50% of AI-generated code containing security weaknesses, managing AI risk is critical. Discover how SCW's Trust Agent: AI provides the real-time visibility, proactive governance, and targeted upskilling needed to scale AI-driven development securely.
The Power of OpenText Application Security + Secure Code Warrior
OpenText Application Security and Secure Code Warrior combine vulnerability detection with AI Software Governance and developer capability. Together, they help organizations reduce risk, strengthen secure coding practices, and confidently adopt AI-driven development.
Secure Code Warrior corporate overview
Secure Code Warrior is an AI Software Governance platform designed to enable organizations to safely adopt AI-driven development by bridging the gap between development velocity and enterprise security. The platform addresses the "Visibility Gap," where security teams often lack insights into shadow AI coding tools and the origins of production code.
Secure code training topics & content
Our industry-leading content is always evolving to fit the ever changing software development landscape with your role in mind. Topics covering everything from AI to XQuery Injection, offered for a variety of roles from Architects and Engineers to Product Managers and QA. Get a sneak peek of what our content catalog has to offer by topic and role.
Resources to get you started
Observe and Secure the ADLC: A Four-Point Framework for CISOs and Development Teams Using AI
While development teams look to make the most of GenAI’s undeniable benefits, we’d like to propose a four-point foundational framework that will allow security leaders to deploy AI coding tools and agents with a higher, more relevant standard of security best practices. It details exactly what enterprises can do to ensure safe, secure code development right now, and as agentic AI becomes an even bigger factor in the future.